Key Takeaways
- A 51% attack occurs when one entity controls more than half of a blockchain's mining hashrate. That control enables double-spends and transaction reversals.
- Bitcoin's hashrate (measured in thousands of exahashes per second) makes a 51% attack irrational on economic grounds.
- Smaller proof-of-work networks with low hashrate and rentable mining power face the highest risk.
- Real-world attacks on Bitcoin Gold, Ethereum Classic, and Verge prove this threat is practical for vulnerable networks.
- Growing network hashrate through distributed mining participation remains the strongest defense against 51% attacks and other crypto attacks.
A 51% attack happens when a single entity controls more than half of a blockchain's mining power. That level of control enables double-spending and transaction reversals. It's one of the most discussed threats in cryptocurrency security. Bitcoin's massive hashrate makes this attack impractical on its network. Smaller proof-of-work chains face a different reality.
What Is a 51% Attack
A 51% attack occurs when one entity gains control of more than half of a blockchain network's mining hashrate. Hashrate is the total computational power used to mine and process transactions on a proof-of-work blockchain.
With majority control an attacker can:
- Double-spend coins by reversing transactions after receiving goods or services
- Block new transactions from confirming on the network
- Reverse recent payments that honest participants already confirmed
- Monopolize block rewards by excluding other miners' blocks
Even majority control has limits. An attacker cannot steal coins from wallets they don't hold private keys for. They cannot create new coins beyond the protocol's rules. They also cannot alter transaction history from before they gained control.
How a 51 Percent Attack Works
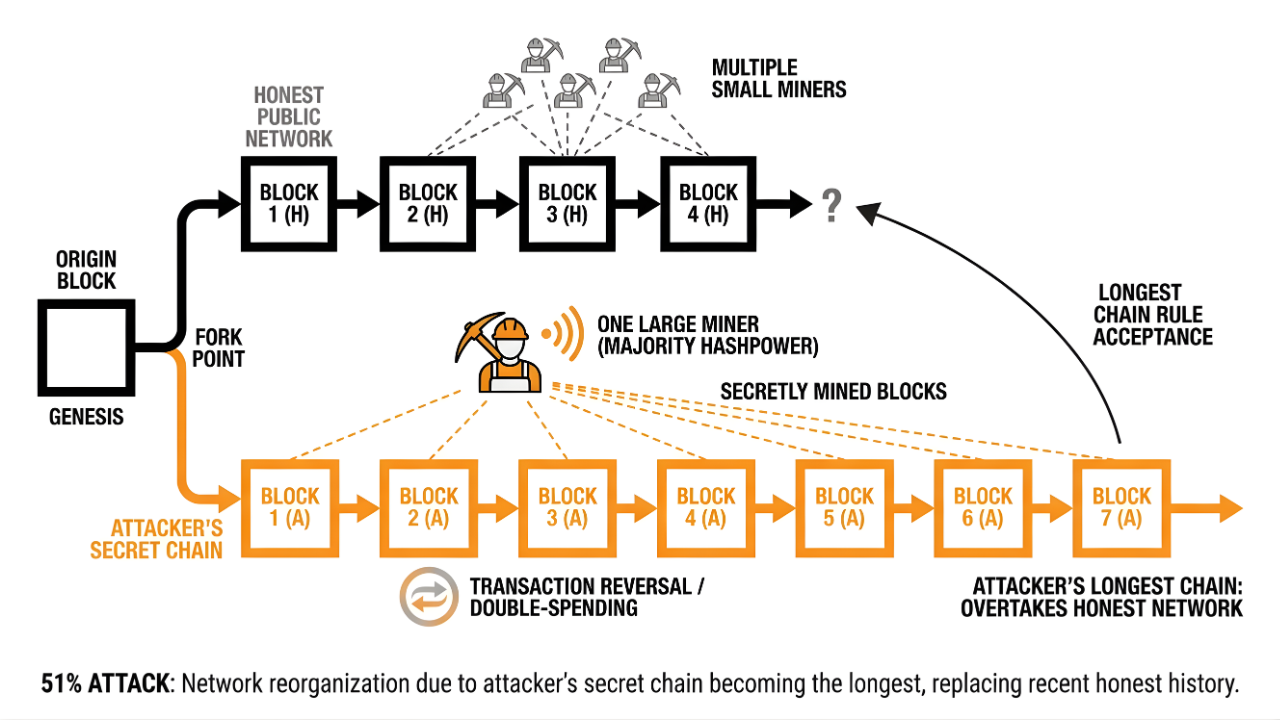
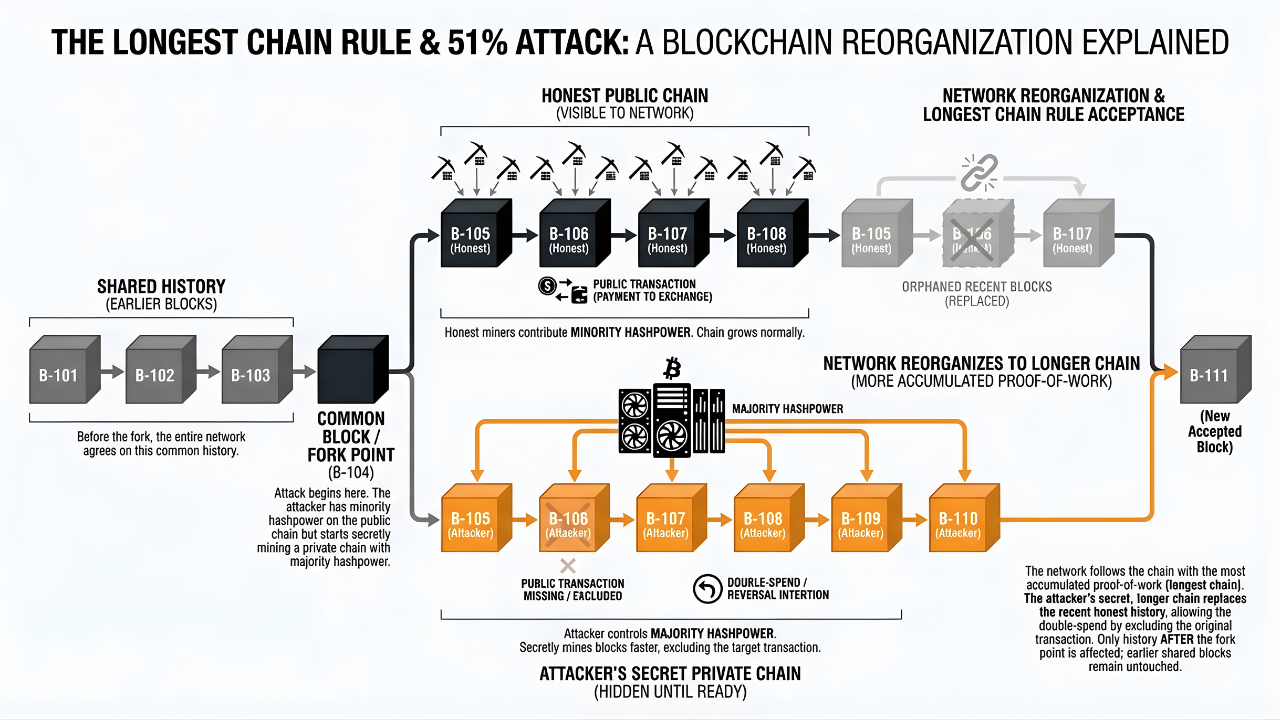
The attack exploits the "longest chain rule." In proof-of-work blockchains the version with the most computational work invested becomes the accepted truth across the network.
Gaining Majority Hashrate Control
The attacker first acquires more mining power than all other miners on the network combined. This can happen through purchasing large amounts of ASIC hardware or renting hashrate from cloud services like NiceHash.
For smaller networks with low total hashrate this barrier can be affordable. For Bitcoin (with over a thousand exahashes per second securing the chain) the cost runs into billions in hardware alone.
Executing Double-Spend Transactions
The attacker spends cryptocurrency on the public blockchain. A common approach: deposit coins on an exchange and trade them for another currency.
At the same time they mine a secret alternate blockchain where that original transaction never happened. Because they control more than 50% of the network's power their hidden chain grows faster than the public one.
Once the secret chain becomes longer they broadcast it. The longest chain rule kicks in and the network accepts the attacker's version. The original transaction disappears. The attacker keeps whatever they received in exchange.
Blocking or Reversing Legitimate Transactions
With majority control an attacker can ignore or reject valid blocks from honest miners. This allows them to censor specific transactions or reverse recent payments by replacing the public chain with their own longer version.
What Happens During a Successful 51% Attack
The consequences hit exchanges, miners, and holders across the entire network.
Double-Spending
The primary financial damage comes from double-spending. Exchanges are attractive targets because an attacker can deposit coins and trade for another currency. They withdraw the proceeds and then reverse the original deposit on the blockchain.
Transaction Reversals
Confirmed transactions can be undone without warning. Users waiting on payments find those transactions erased from the blockchain. This undermines the core promise of the technology: transaction finality.
Loss of Network Confidence
Successful attacks trigger a sharp decline in trust and token price. Some projects never recover their reputation or market value after a major attack.
Disrupted Miner Revenue
Blocks mined by honest participants get orphaned (discarded) when the attacker releases their longer chain. Honest miners lose the block rewards they earned. If attacks become frequent the remaining legitimate miners may abandon the network. That makes future attacks even cheaper to execute.
How Much Does a 51% Attack Cost
The cost depends on the network's total hashrate, hardware availability, electricity rates, and how long the attacker needs to maintain control.
| Factor | Impact on Attack Cost |
|---|---|
| Network total hashrate | Higher hashrate = higher cost |
| Hardware availability | Scarce ASICs make acquisition difficult |
| Electricity rates | Lower rates reduce ongoing operational costs |
| Attack duration | Longer attacks multiply expenses |
For Bitcoin the numbers are staggering. Acquiring majority control would require billions in hardware plus millions per day in electricity. Smaller networks tell a different story. Some are vulnerable to attacks costing a few thousand dollars per hour through rented hashrate.
The economic calculation is simple. If the potential profit from double-spending exceeds the attack cost the network becomes a target.
Real-World 51% Attack Examples
Several proof-of-work networks have suffered successful 51% attacks. These cases prove the threat is more than theoretical.
Bitcoin Gold
Bitcoin Gold (a fork of Bitcoin) suffered multiple attacks between 2018 and 2020. Its low hashrate relative to Bitcoin made it an attractive target. The MIT Digital Currency Initiative tracked these events as part of broader research into chain reorganizations across smaller networks.
Ethereum Classic
Ethereum Classic experienced repeated attacks in 2019 and 2020. Exchanges responded by halting deposits and requiring hundreds of confirmations before accepting ETC transactions.
Verge
Verge (a privacy-focused cryptocurrency) was attacked multiple times in 2018. Vulnerabilities in its mining algorithm allowed attackers to gain majority control with modest hashrate.
These examples share a common thread. Smaller networks with lower hashrate and limited miner diversity face the highest risk of crypto attacks.
Which Crypto Networks Are Vulnerable to Attack 51
Smaller proof-of-work networks with low hashrate and limited miner participation face the highest risk. Several factors determine vulnerability:
- Low total hashrate: Less computational power securing the network means a lower attack cost
- Proof-of-work consensus: PoW networks are more susceptible than proof-of-stake systems (which require capital rather than hashrate)
- Hashrate available for rent: When mining power can be rented the attacker doesn't need to own hardware
- Limited miner diversity: Networks where a few pools control most hashrate face higher collusion risk
Newer altcoins and Bitcoin forks are the most common targets. Their smaller communities and lower hashrates make them easier to overpower.
Is Bitcoin Safe from a 51% Attack
Bitcoin's massive hashrate makes a 51% attack impractical on economic and logistic grounds. No successful 51% attack has ever occurred on the Bitcoin network.
The math explains why. Acquiring majority control would require:
- Tens of billions of dollars in ASIC mining hardware
- Months (or years) to manufacture and deploy equipment
- Massive electrical infrastructure to power the machines
- Ongoing operational costs measured in millions per day
Even nation-states would struggle to assemble that level of resources. And here's the economic paradox: anyone with enough capital to attack Bitcoin would profit more by mining honest blocks.
The attack would also be visible to the network within minutes. Exchanges would halt transactions. The price would crash. The attacker's stolen coins would lose most of their value before they could be sold.
How to Prevent 51 Percent Attacks
Networks and their participants can deploy several defenses against these crypto attacks.
1. Increasing Network Hashrate
The most effective defense is growing total hashrate. More miners and wider distribution raise the cost barrier for attackers. Every additional terahash of honest mining power makes majority control harder to achieve.
Professional Bitcoin mining operations contribute legitimate hashrate that strengthens network defenses on a continuous basis.
2. Requiring More Transaction Confirmations
Exchanges and merchants can wait for more block confirmations before considering a transaction final. Bitcoin's standard recommendation is 6 confirmations (about 60 minutes).
After major attacks on smaller coins some exchanges now require 100 or more confirmations. That can mean waiting days before deposits become available.
3. Switching Consensus Mechanisms
Some networks have moved from proof-of-work to proof-of-stake. In PoS systems an attacker needs a majority of the network's staked tokens rather than hashrate.
This approach has tradeoffs. It eliminates traditional 51% attacks but introduces different security considerations and changes the network's economic model.
4. Implementing Penalty Systems
Some protocols penalize miners who submit competing chains or engage in suspicious behavior. Finality checkpoints can also limit how far back an attacker can rewrite history. These mechanisms create a direct cost for malicious actions.
Why Bitcoin Mining Remains Secure Against Crypto Attacks
Bitcoin's security stems from its massive hashrate and the economic incentives that make attacks irrational. The network has operated since 2009 without a single successful 51% attack.
Professional mining operations are critical to this security model. By contributing legitimate hashrate miners strengthen the network's defenses while earning rewards. Every hosted machine adds to the cost an attacker would need to overcome.
Explore hosted Bitcoin mining with Simple Mining →
Read More on Simple Mining Insights →
FAQs about 51% Attacks
What is the difference between a 51% attack and selfish mining?
A 51% attack requires majority hashrate control to manipulate the blockchain. Selfish mining is a strategy where miners with less than majority power withhold valid blocks in secret to earn more rewards than their hashrate share would allow. The two exploit different vulnerabilities in proof-of-work consensus.
Can mining pools execute a 51% attack?
A mining pool controlling over 50% of network hashrate could attempt an attack in theory. However, individual miners in the pool can switch pools if they detect malicious behavior. The reputational damage would also destroy the pool's business.
How long do 51% attacks last?
Most documented attacks last a few hours to a couple of days. Sustaining majority hashrate control is expensive. Networks respond fast with countermeasures like halting exchange deposits and coordinating honest miners to reject the attacker's chain.
Do 51% attacks affect coins stored in personal wallets?
Attackers cannot steal coins from wallets they don't hold private keys for. They can only reverse their own recent transactions. Your funds remain safe unless you accepted a payment from an attacker that later gets reversed.
By Josh Heine, Content Strategist at Simple Mining
Published: July 10, 2024
Modified: March 9, 2026
