Key Takeaways
- KYC stands for "Know Your Customer," a mandatory process to verify identity and assess risk before establishing a financial relationship.
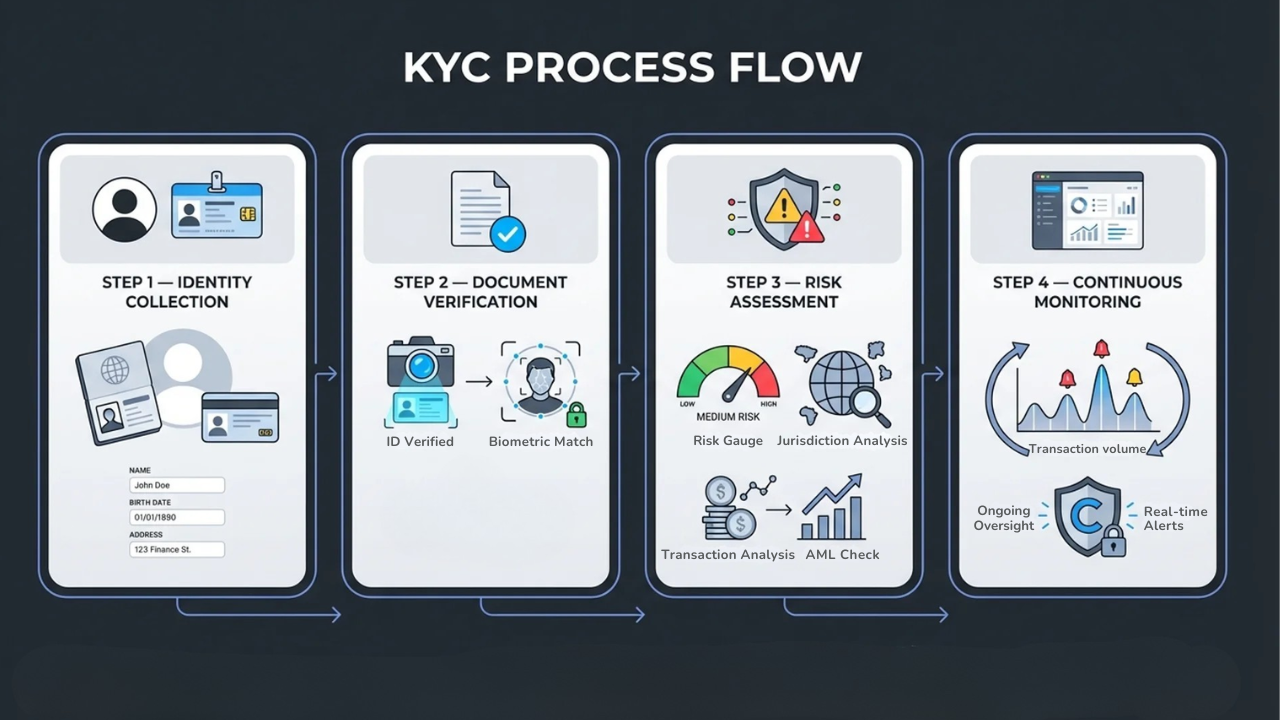
- The verification process follows four steps: identity collection, document verification, risk assessment, and continuous monitoring.
- KYC is a component of Anti-Money Laundering (AML), not a replacement for a full AML program.
- In Bitcoin mining, KYC comes down to two decisions: pool selection and wallet hygiene. A non-custodial pool plus a fresh wallet with no exchange history means non-KYC mining.
- Your hosting provider does not determine your KYC status. Your pool and wallet do.
KYC stands for "Know Your Customer." It is the mandatory verification process financial institutions and businesses use to confirm a customer's identity before establishing a relationship. You complete KYC every time you submit a driver's license to open a bank account or upload a selfie to activate a crypto exchange. This guide covers how the process works, what documents you need, and why KYC matters whether you trade Bitcoin or host miners.
What Does KYC Mean
KYC (short for "Know Your Customer" or "Know Your Client") is a standardized process to verify a customer's identity, background, and risk level. The term originates in banking regulation but now applies to any business that handles financial transactions.
The core purpose is simple: confirm people are who they claim to be. Without KYC, bad actors can move illicit funds through financial systems undetected. Banks, exchanges, and service providers use KYC to screen customers before granting account access. The process also protects customers by making verified accounts harder to compromise.
- KYC meaning: A standardized process to verify customer identity and assess risk
- Also known as: Know Your Client, customer due diligence
- Primary purpose: Preventing financial crime while protecting institutions and customers
KYC verification happens during account onboarding. It can also be triggered when suspicious activity appears or when regulations require periodic re-checks. Over the past two decades, KYC requirements have evolved from basic ID checks into comprehensive risk management frameworks.
Why KYC Matters for Businesses and Customers
KYC prevents fraud, money laundering, and terrorism financing. For businesses, compliance is not optional. Reported fraud losses reached $12.5 billion in 2024, a 25% increase in a single year. Regulators respond to those numbers with enforcement. Institutions that fail KYC obligations face fines that can reach billions of dollars.
For customers, KYC adds a layer of protection. Verified platforms are harder for criminals to exploit. When every participant on a service has been vetted, the entire ecosystem becomes safer.
| Benefit | For Businesses | For Customers |
|---|---|---|
| Security | Fraud prevention, regulatory compliance | Account protection, reduced identity theft |
| Trust | Maintained banking relationships | Confidence in platform legitimacy |
| Risk | Legal liability reduction | Safer transaction environment |
How the Know Your Customer Process Works
The KYC verification process follows four steps: identity collection, document verification, risk assessment, and continuous monitoring. Specific requirements vary by institution, but the sequence stays consistent across industries.
Step 1. Collect Identity Information
The process starts with gathering customer data. For individuals, this includes full legal name, date of birth, residential address, and a government-issued identification number. For businesses, KYC extends to company registration details, ownership structure, and information about beneficial owners.
Step 2. Verify Submitted Documents
Institutions authenticate submitted documents against official databases. Many platforms now use electronic verification (eKYC) to complete this step in minutes rather than days. eKYC involves document scanning, facial recognition, and automated database cross-referencing. Complex applications or flagged submissions may still require manual review.
Step 3. Assess Customer Risk Level
Not every customer presents the same risk. Institutions evaluate financial behavior, geographic location, and industry exposure to assign a risk category. A politically exposed person (PEP) or someone from a high-risk jurisdiction faces additional scrutiny compared to a standard retail customer.
Step 4. Monitor Activity Continuously
KYC is not a one-time event. After onboarding, institutions monitor customer transactions for suspicious patterns. Periodic re-verification can be triggered by risk level changes, updated regulations, or new information about the customer.
Three Core Components of KYC Compliance
KYC compliance rests on three pillars that work together within the broader know your customer procedures framework.
Customer Identification Program
The Customer Identification Program (CIP) is the foundation. CIP establishes minimum standards for collecting and verifying identity information. Under U.S. banking regulations, every financial institution must maintain a CIP. Requirements include collecting name, date of birth, address, and identification number, then verifying that data through documents or non-documentary methods.
Customer Due Diligence
Customer Due Diligence (CDD) goes beyond basic identification. CDD involves understanding the nature and purpose of the customer relationship and establishing a baseline risk profile. It answers core questions: What is the expected transaction volume? What is the source of funds? Does the stated purpose align with actual activity?
Enhanced Due Diligence
Enhanced Due Diligence (EDD) applies to higher-risk customers. This includes PEPs, customers in high-risk jurisdictions, and entities with complex ownership structures. EDD requires deeper investigation, more frequent monitoring, and senior management approval. The goal is proportionate scrutiny based on actual risk.
What Documents Are Required for KYC Verification
Most KYC processes require a government-issued photo ID, proof of address, and (for businesses) corporate registration documents. Specific requirements vary by institution and jurisdiction.
Government-Issued Photo ID
A valid passport, driver's license, or national ID card serves as primary identification. The document must be current and legible. Some platforms accept multiple forms of ID while others require a specific document.
Proof of Address
Address verification requires a recent utility bill, bank statement, or lease agreement. Most institutions require documents dated within the last 90 days. The address should match what you provided during registration. Discrepancies can delay the process.
Business Verification Documents
Corporate entities must provide certificates of incorporation, articles of organization, and beneficial ownership information. Beneficial ownership rules require identifying any individual who owns 25% or more of a company or who exercises significant control.
KYC vs AML and How They Work Together
KYC is a subset of Anti-Money Laundering (AML). KYC focuses on verifying customer identity. AML is the broader organizational program designed to prevent financial crime. AML includes KYC plus transaction monitoring, suspicious activity reporting, and compliance governance.
| Aspect | KYC | AML |
|---|---|---|
| Focus | Customer identity verification | Preventing money laundering |
| Scope | Individual or entity level | Organization-wide program |
| Relationship | A component within AML | Includes KYC, monitoring, and reporting |
Think of KYC as one tool in the AML toolkit. Effective AML requires KYC, but KYC alone does not constitute a complete AML program. The Financial Action Task Force (FATF) sets international standards that influence both KYC and AML regulations in over 190 countries.
Who Must Comply with KYC Regulations
Banks, cryptocurrency exchanges, and Bitcoin mining providers all implement KYC to meet regulatory requirements and maintain banking relationships. The scope extends well beyond traditional finance.
Banks and Financial Institutions
Traditional banks face the most comprehensive KYC requirements. The Bank Secrecy Act, USA PATRIOT Act, and FINRA rules establish baseline standards. Non-compliance can result in fines reaching hundreds of millions of dollars.
Cryptocurrency Exchanges and Platforms
Most cryptocurrency platforms require KYC verification before users can trade, withdraw funds, or conduct large transactions. Regulatory pressure has driven this shift. Exchanges that want to operate in major markets maintain KYC as standard practice.
Bitcoin Mining and Hosting Providers
KYC in Bitcoin mining is not about the hosting provider. It is about the pool you choose and the wallet you use. A hosting provider powers and maintains your hardware. Your pool and wallet determine whether your mining activity carries a KYC footprint.
Miners who want non-KYC mining pair a non-custodial pool with a fresh wallet that has no exchange history. Miners who plan to sell through centralized exchanges will encounter KYC at that step. The hosting layer sits outside this decision entirely.
KYC in Crypto and Bitcoin Mining
KYC is common across the cryptocurrency ecosystem. While Bitcoin itself is permissionless at the protocol level, certain services require identity verification before granting access.
Centralized exchanges are the most obvious example. You cannot trade or withdraw funds on most major exchanges without completing KYC. That verification is tied to your account and every wallet address you use within it.
For Bitcoin miners, KYC comes down to two decisions: pool selection and wallet hygiene.
Pool selection determines whether your mining payouts touch a KYC service. Custodial pools that require account registration tie your hashrate to a verified identity. Non-custodial pools like Ocean pay directly to your wallet with no account, no registration, and no identity checks.
Wallet hygiene is the other half. A fresh wallet with no prior exchange history keeps your mining payouts separate from any KYC trail. If you have ever sent Bitcoin to that wallet from a centralized exchange, the exchange already has a record connecting your identity to that address. At that point, the wallet carries a KYC footprint regardless of which pool you use.
Miners who want to mine without KYC can do so by pairing a non-custodial pool with a clean wallet. Miners who prefer the convenience of custodial pools or plan to sell on exchanges will encounter KYC at those touchpoints. The choice belongs to the miner.
Working with a Compliant Bitcoin Mining Provider
KYC exists to keep financial systems accountable. For Bitcoin miners, whether your operation carries a KYC footprint comes down to pool selection and wallet hygiene, not your hosting provider.
Simple Mining keeps your machines running at 98% average uptime with precision billing and 12 months of free repairs. You choose your pool. You control your wallet. Start your 7-day free trial to see how it works.
FAQs About Know Your Customer Verification
How long does KYC verification typically take?
KYC verification ranges from a few minutes with electronic verification (eKYC) to several business days for manual review. The timeline depends on document quality, application complexity, and the institution's process. Most modern platforms complete standard verifications within 24 to 48 hours.
What happens if KYC verification fails?
Failed verification results in a request to resubmit clearer documents or provide additional information. Common issues include blurry images, expired documents, or mismatched addresses. Contact the institution's support team to resolve discrepancies.
Is KYC required to start Bitcoin mining with a hosting provider?
KYC in Bitcoin mining is determined by your pool and wallet, not your hosting provider. If you use a non-custodial pool like Ocean and a fresh wallet with no exchange history, your mining payouts carry no KYC footprint. If you sell mined Bitcoin on a centralized exchange, KYC applies at that step.
Can KYC verification be completed without a passport?
Yes. Most institutions accept alternative government-issued photo identification such as a driver's license or national ID card. Requirements vary by provider and jurisdiction. Check specific document requirements before starting verification to avoid delays.
How is personal information protected during KYC verification?
Compliant institutions use encryption, secure storage, and data protection policies aligned with privacy regulations. Your information is stored in encrypted databases with strict access controls. Ask your provider about their data handling practices before submitting documents.
By Josh Heine, Content Strategist at Simple Mining
Published: September 18, 2024
Modified: March 6, 2026
