This short video breaks down what a hash is, how cryptographic hash functions work, and why hashing matters for Bitcoin mining and network security. Below you'll find the full transcript and FAQs. For a deeper look at SHA-256, hashrate, and how hashing fits into the mining process, read the full written guide on what a hash is.
Read the full guide: What is a Hash?
Full Transcript
What is a hash?
If you mine Bitcoin, the term "hash" is everywhere: hashrate, hashprice, terahash, and more. Hashing matters because it relates to machine efficiency, profitability, and network security.
You've likely heard a surface-level explanation that a hash is a complex computer guess at a particular combination. That is true at a basic level, but let's expand. Bitcoin uses hashing to generate addresses, provide proof of work, and sign transactions.
If you believe Bitcoin will change money as we know it, understanding how hashing works will increase your confidence as a network participant.
Here are the basics. Satoshi was a hashing and cryptography fanatic. A hash is the output of a hash function. A hash function is a mathematical function (like y = mx + b) but more interesting.
Baking a cake is a good analogy. The inputs are flour, sugar, and eggs. The function is the transformation of the ingredients through mixing and baking. The output is the finished cake.
The big idea is this: an input passes through a hash function and produces an output. The input could be any message. The output is the hash of that message.
When you see a mining machine that runs 200 terahashes per second, that means it is making 200 trillion hash attempts per second.
What makes a hash function cryptographic? First, it must be computationally feasible to convert an input into a hash output. Second, it must be computationally infeasible to guess the input based only on the output.
Third, the input must deterministically produce the same hash output every time. "Hello" will always return the same output. Fourth, each output should be unique, meaning even small changes in the input create a completely different hash. "Hello" and "Hello!" will produce entirely different hashes. Fifth, it should be computationally infeasible to find two different inputs that produce the same hash output.
For context, Bitcoin uses SHA-256, a secure hash algorithm with a 256-bit output. SHA-256 is not just used in Bitcoin. It is a global cybersecurity standard.
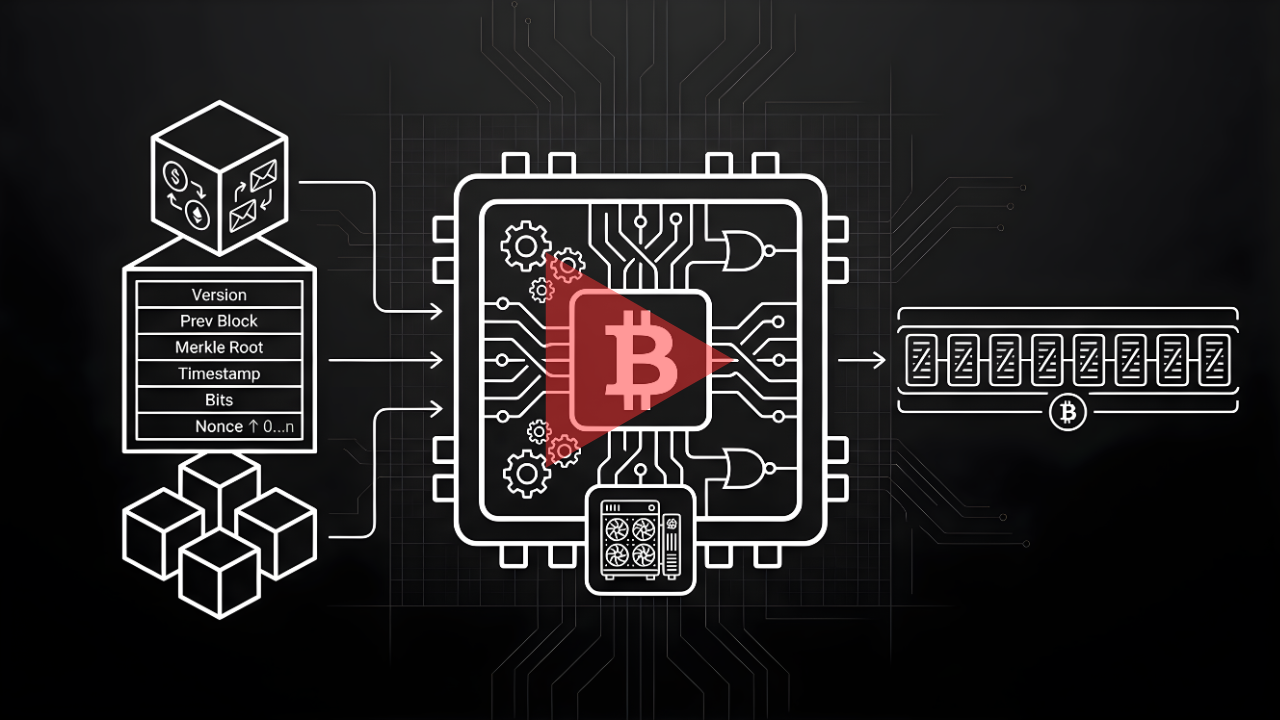
Proof of work is one example of how miners use hashing. It is how a miner proves they completed the work to find a block. This is done by hashing the block header, which includes information such as the software version, a timestamp, and the previous block's hash.
This is also what makes Bitcoin transactions a chain. Each block is connected to the previous one. This prevents transaction history from changing because altering a previous block would require redoing the proof of work for every block that comes after it.
So the hash (and the hash of all blocks that follow) makes the longest chain the truth because it contains the most proof of work. Remember, for a hash to be cryptographic, it must be practically impossible to determine the input from the hash output.
The only realistic method would be to guess and check, which would be like finding a needle in a haystack of 2 to the 256th power hashes (roughly one hundred fifteen quattuorvigintillion possibilities).
To learn more about Bitcoin mining, visit simplemining.io.
FAQs
What hash function does Bitcoin use?
Bitcoin uses SHA-256 (Secure Hash Algorithm, 256-bit). SHA-256 is a global cybersecurity standard used far beyond Bitcoin, from SSL certificates to file verification. Every hash output is a 256-bit (64-character hexadecimal) string.
What does hashrate mean?
Hashrate measures how many hash attempts a mining machine makes per second. A machine rated at 200 TH/s (terahashes per second) is making 200 trillion guesses per second. Higher hashrate means a greater chance of finding the next block and earning the block reward.
What makes a hash function cryptographic?
A cryptographic hash function meets five properties: it's fast to compute, impossible to reverse, deterministic (same input always produces the same output), collision-resistant (no two inputs should produce the same output), and avalanche-sensitive (a tiny change in the input creates a completely different hash).
How does hashing relate to proof of work?
Miners hash the block header (which includes the previous block's hash, a timestamp, and other data) over and over with different values until the output meets a target set by the network. That valid hash is the "proof" that computational work was performed. This process secures every block in the Bitcoin blockchain.
By Josh Heine, Content Strategist at Simple Mining
Published: November 2, 2024
Modified: March 9, 2026