Key Takeaways
- A hash is a fixed-length digital fingerprint produced by running data through a one-way mathematical function. It cannot be reversed.
- Bitcoin uses the SHA-256 hashing algorithm for all mining, block creation, and transaction verification.
- Hashrate (measured in TH/s for individual miners and EH/s for the network) directly determines your probability of earning block rewards.
- ASIC miners dominate Bitcoin mining because they are purpose-built for SHA-256, outperforming general-purpose hardware by orders of magnitude.
- Mining profitability depends on the relationship between hashrate, energy efficiency (J/TH), and electricity cost. Professional hosting reduces operational risk and simplifies the math.
A hash is a fixed-length string of characters that acts as a unique digital fingerprint for any piece of data. In Bitcoin mining, hashes are the core unit of work. Miners compute trillions of them per second, racing to find one that meets the network's difficulty target. This guide covers how hashing works, why Bitcoin uses SHA-256, and what hashrate means for mining profitability.
What Is a Hash
A hash is a fixed-length string of characters produced by running data through a mathematical function. Think of it as a unique digital fingerprint for any piece of information.
Any input (a word, a file, a Bitcoin transaction) produces a scrambled output that always looks the same length. Change even one character, and you get a completely different hash. This property makes hashing the foundation of blockchain security.
- Hash: A fixed-length string of characters produced by running data through a mathematical function.
- Hash value: The output string itself, which acts as a unique digital fingerprint for the input data.
- Hashed data: The original data after it has been processed by a hash function.
How Does Hashing Work
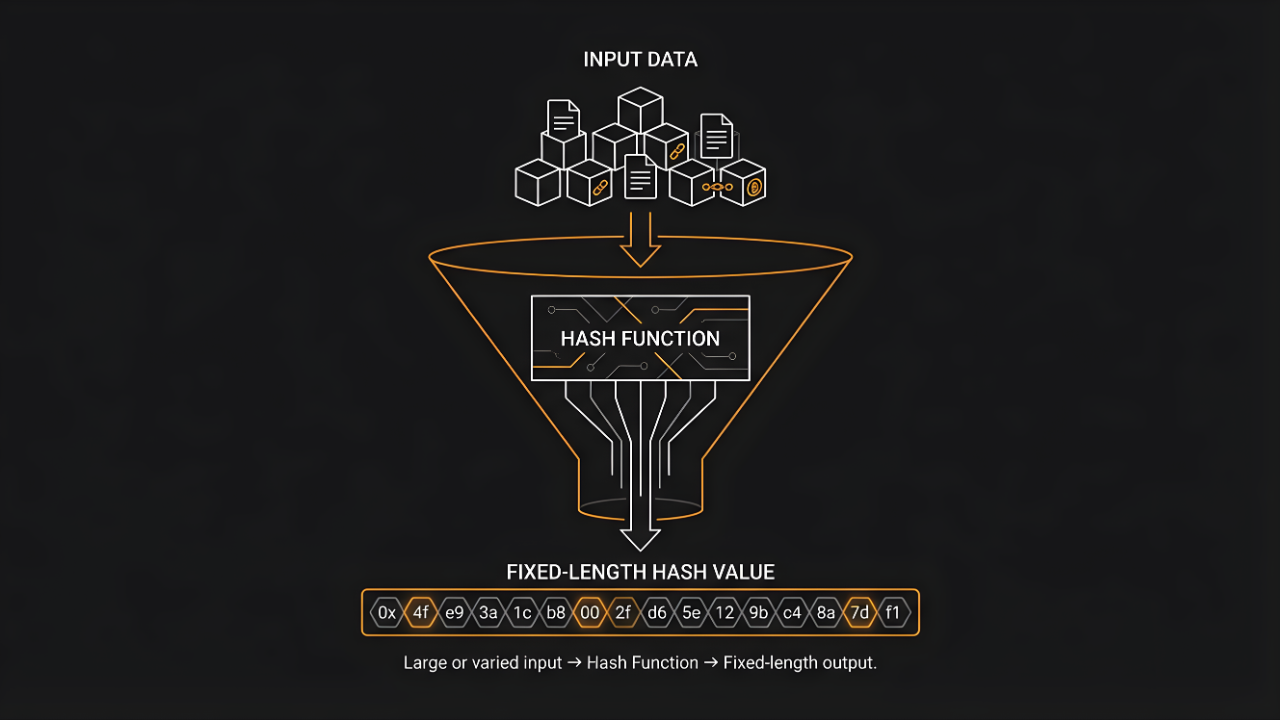
Hashing feeds data through a one-way mathematical function that produces a fixed-length output. The critical thing to understand: you cannot reverse the process.
Input Data
Any data can be hashed. Text, numbers, files, Bitcoin transactions. The input can be any size, from a single letter to an entire database.
Hash Function Processing
The hash function is the algorithm that scrambles the input. It applies complex mathematical operations to transform data into something unrecognizable. The same input always produces the same output, without exception.
Hash Value Output
The output is always a fixed-length string regardless of input size. Even a tiny change creates a completely different hash value. Cryptographers call this the avalanche effect.
Input: "Hello" → Hash: 185f8db32271fe25f561a6fc938b2e...
Input: "hello" → Hash: 2cf24dba5fb0a30e26e83b2ac5b9e...
One capital letter changed. Entirely different 64-character output.
What Is a Hash Function
A hash function is the specific algorithm that converts input data into a fixed-length hash value. It's deterministic: the same input always yields the same output.
Key Properties of Hash Functions
- Deterministic: Same input always produces the same hash output.
- Fixed output length: Hash value is always the same size, regardless of input size.
- Fast to compute: Output is calculated in milliseconds.
- Collision-resistant: Practically impossible to find two inputs that produce the same hash.
- Avalanche effect: A tiny input change creates a completely different output.
Why Hash Functions Are One-Way
Reversing a hash means guessing every possible input until you find a match. For SHA-256, that could take longer than the age of the universe. Even if someone sees the hash, they cannot work backward to discover the original data.
Common Hashing Algorithms
Different hashing algorithms serve different purposes. Bitcoin relies on SHA-256 for all mining and transaction verification.
SHA-256
SHA-256 is Bitcoin's hashing algorithm. It produces a 256-bit (64-character hexadecimal) output and remains the industry standard for cryptographic security. The algorithm is computationally intensive by design, which makes it ideal for proof-of-work mining.
Scrypt and Other Mining Algorithms
Other cryptocurrencies use different algorithms. Scrypt (Litecoin) is memory-intensive. Ethash (Ethereum's former PoW algorithm) was memory-hard.
| Algorithm | Used By | Key Characteristic |
|---|---|---|
| SHA-256 | Bitcoin | Computationally intensive; ideal for ASIC miners |
| Scrypt | Litecoin | Memory-intensive; designed to be more ASIC-resistant |
| Ethash | Ethereum Classic | Memory-hard; also designed to resist ASICs |
For Bitcoin mining, SHA-256 is the only algorithm that matters.
How Hashing Powers Bitcoin Mining
Bitcoin miners compete to find a valid hash by running SHA-256 trillions of times per second until the output meets the network's difficulty target.
What Is Proof-of-Work
Proof-of-work is Bitcoin's consensus mechanism. Miners must solve hash puzzles before adding a new block to the blockchain. The "work" is computing countless hashes until one meets the difficulty requirements.
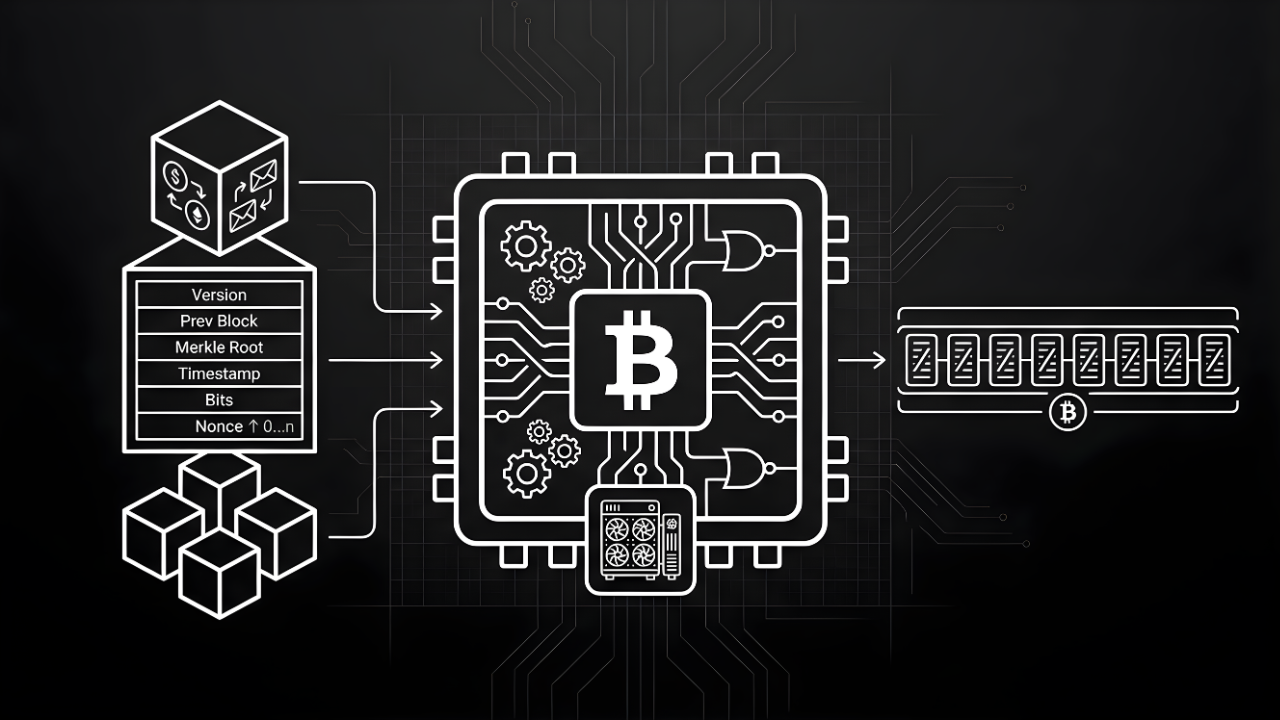
How Miners Solve Hashes
Miners combine transaction data with a nonce (number used once), hash the combination, and check if the output starts with enough leading zeros. If not, they increment the nonce and try again.
When a miner finds a valid hash, they broadcast the block and earn the block reward plus transaction fees. In our repair center, we see what happens when a hashboard fails mid-operation. A single dead board on an Antminer S21 can drop the machine from 200 TH/s to 130 TH/s overnight. Our dashboard flags these drops within minutes so the machine can be pulled and repaired on-site.
Why Bitcoin Uses SHA-256
SHA-256 is collision-resistant, fast enough for mining, and impossible to reverse. Satoshi Nakamoto chose it deliberately. More than fifteen years later, it remains unbroken.
What Is Hashrate and Why It Matters
Hashrate measures how many hashes a miner computes per second. It directly determines your probability of earning block rewards.
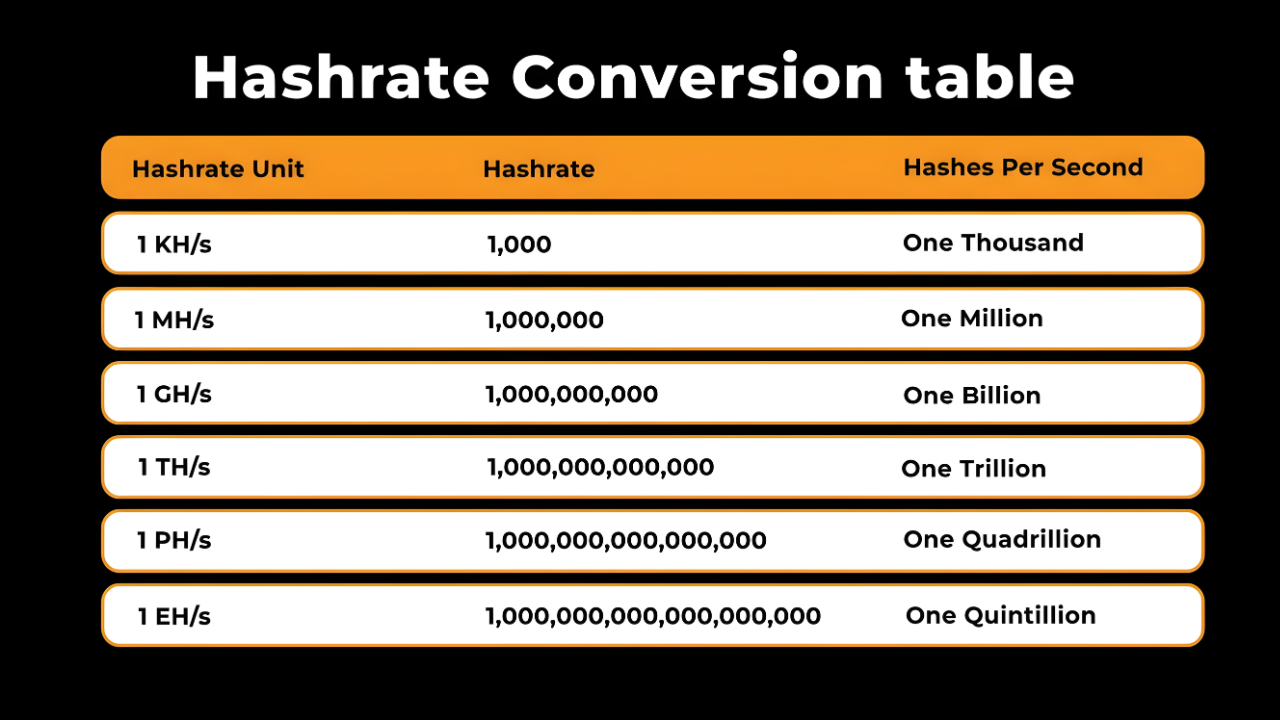
Understanding TH/s and EH/s
- TH/s: Terahashes per second (1 trillion hashes). Used for individual ASIC miners.
- PH/s: Petahashes per second (1 quadrillion hashes). Used for large mining operations.
- EH/s: Exahashes per second (1 quintillion hashes). Used for the full Bitcoin network.
How Hashrate Affects Mining Rewards
Your share of total network hashrate determines your probability of earning rewards. This is why mining pools exist. Instead of waiting months for a solo block, pool miners receive smaller, more frequent payouts proportional to their contributed hashrate.
Why ASIC Miners Dominate Hashing
ASICs (Application-Specific Integrated Circuits) are purpose-built for SHA-256. A modern ASIC outperforms a high-end gaming GPU by roughly 10,000x for Bitcoin mining. This is why serious mining requires specialized hardware and often hosting services that handle the operational complexity.
One thing investors often misunderstand: the nameplate hashrate on a spec sheet isn't always what the machine delivers at the wall. Temperature, firmware, and board health all affect real-world output. We stress-test every machine after repair to confirm it's hitting spec before it goes back on the rack.
Hashing vs Encryption
Hashing is a one-way process that verifies data integrity. Encryption is a two-way process that protects data confidentiality using a key.
| Feature | Hashing | Encryption |
|---|---|---|
| Reversibility | One-way (cannot be reversed) | Two-way (can be decrypted with a key) |
| Purpose | Verify data integrity | Protect data confidentiality |
| Key Required | No | Yes |
| Output Length | Fixed | Variable |
Bitcoin uses hashing for mining and transaction verification. It uses encryption (specifically, elliptic curve cryptography) for wallet security and digital signatures.
Why Hashing Matters for Mining Profitability
The relationship between hashrate, energy efficiency, and electricity cost determines whether mining is profitable. More efficient miners produce more hashes per watt consumed.
| Metric | Efficient Miner (13.5 J/TH) | Older Miner (21 J/TH) |
|---|---|---|
| Hashrate | 200 TH/s | 200 TH/s |
| Power Draw | 2.7 kW | 4.2 kW |
| Monthly kWh (95% uptime) | ~1,847 kWh | ~2,873 kWh |
| Monthly Power Cost ($0.075/kWh) | ~$139 | ~$215 |
Same hashrate, but the efficient machine saves over $75/month. Multiply that across a fleet, and the numbers compound fast. Professional hosting handles the operational complexity (power, cooling, repairs) so miners can focus on returns.
Explore Simple Mining's hosting and use our profitability calculator to model your returns →
FAQs About Hashing in Cryptocurrency Mining
What is a hash in simple terms?
A hash is a unique fixed-length digital fingerprint created by running any data through a mathematical function. It verifies data integrity without revealing the original content. The same input always produces the same hash, but you cannot work backward from the hash to discover the input.
Can you reverse a hash to recover the original data?
No. Hash functions are designed to be one-way, making it computationally impossible to work backward from a hash value to the original input. This is what makes hashing secure for passwords, blockchain verification, and mining.
What happens when two different inputs produce the same hash?
This rare event is called a collision. Modern algorithms like SHA-256 are designed to make collisions virtually impossible to find intentionally. Older algorithms like MD5 have known collision vulnerabilities, which is why Bitcoin uses SHA-256.
How many hashes can a Bitcoin miner compute per second?
Modern ASIC miners compute trillions of hashes per second, measured in TH/s. Current-generation machines range from roughly 100 TH/s to over 1,000 TH/s depending on model (e.g., air-cooled vs. hydro-cooled) and efficiency.
What is mining difficulty and how does it relate to hashing?
Mining difficulty is a network-adjusted target that determines how hard it is to find a valid hash. As more hashrate joins the network, difficulty increases to maintain consistent 10-minute block times. When hashrate drops, difficulty decreases. This adjustment happens approximately every two weeks (2,016 blocks).
By Josh Heine, Content Strategist at Simple Mining
Published: June 13, 2024
Modified: March 9, 2026